Updating NGINX to the development branch (on Ubuntu) to get more frequent updates and features over the stable branch
Aside
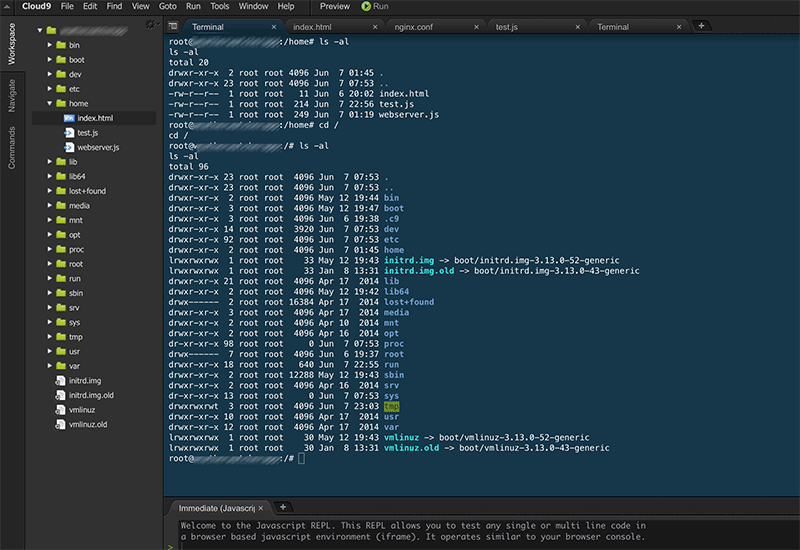
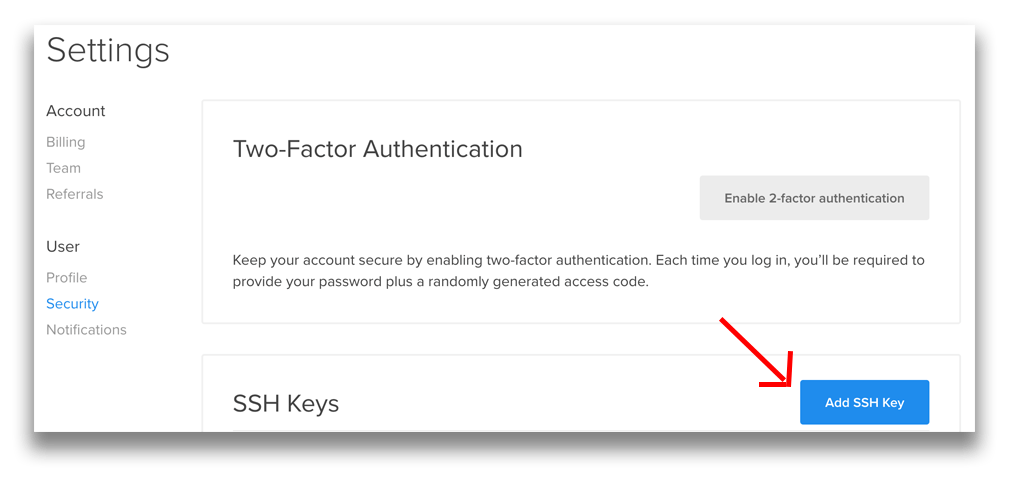
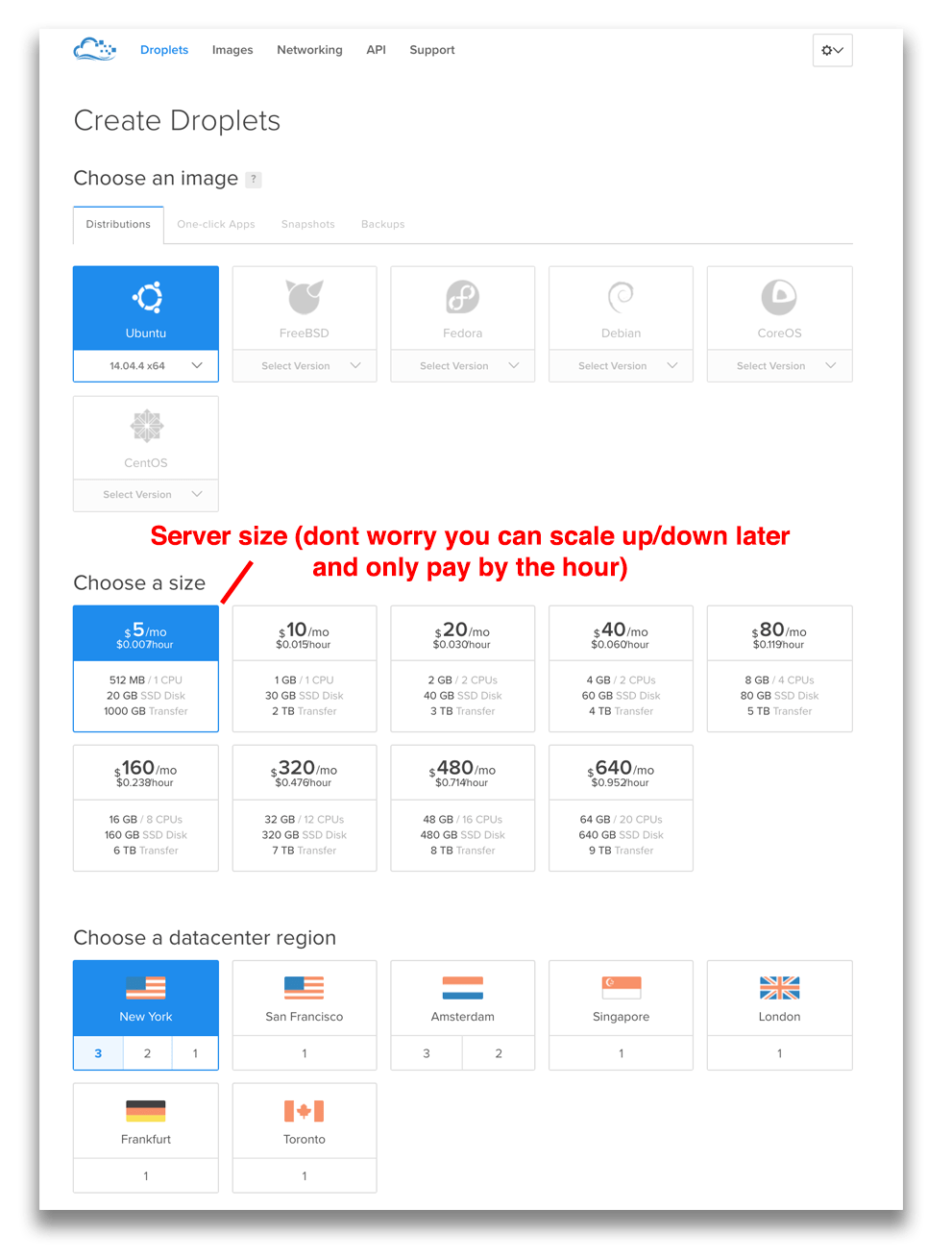
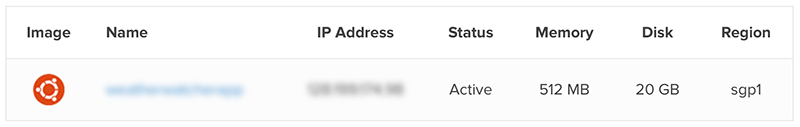
I have a number of guides on moving away from CPanel, Setting up VM’s on UpCloud, AWS, Vultr or Digital Ocean along with installing and managing WordPress from the command line. View all recent posts here https://fearby.com/all/
Now on with the post
Warning
Backup your Nginx and Server before making any changes. The Nginx development branch is quite stable but anything can happen. If your site is mission-critical then stay on the stable branch.
Nginx Branches
By default, you will most likely get the stable branch of Nginx when instaling and updating Nginx. I have been running the stable version for the last few years but was made aware of a DDoS vulnerability in Nginx.
Here is a good write-up on development merges into the stable branch.
Nginx Updates
Widely-used #Nginx server releases versions 1.15.6 and 1.14.1 to patch two HTTP/2 implementation vulnerabilities that might cause excessive memory consumption (CVE-2018-16843) & CPU usage (CVE-2018-16844), allowing a remote attacker to perform #DoS attackhttps://t.co/1Z3JoghoBr pic.twitter.com/qQ3pOFD1Lk
— The Hacker News (@TheHackersNews) November 9, 2018
I was aware recently of a DDoS bug affecting Nginx and the recommendation was to update ot Nginx 1.15.6 development branch (or 1.14.1 stable branch).
A few days ago no 1.14.1 update was available but a 1.15.6 was, should I switch to the development branch to get updates earlier?
Reminder to update your #nginx installations to the 1.14.1 stable or the 1.15.6 mainline versions for critical security patches released this week. #NGINXPlus customers, see instructions for updating based on the patch released 10/30 https://t.co/KitsOWIJkb
— NGINX, Inc. (@nginx) November 8, 2018
Recent Nginx Changes
Here are the recent changes to Nginx: http://nginx.org/en/CHANGES
Changes with nginx 1.15.6 06 Nov 2018
*) Security: when using HTTP/2 a client might cause excessive memory
consumption (CVE-2018-16843) and CPU usage (CVE-2018-16844).
*) Security: processing of a specially crafted mp4 file with the
ngx_http_mp4_module might result in worker process memory disclosure
(CVE-2018-16845).
*) Feature: the "proxy_socket_keepalive", "fastcgi_socket_keepalive",
"grpc_socket_keepalive", "memcached_socket_keepalive",
"scgi_socket_keepalive", and "uwsgi_socket_keepalive" directives.
*) Bugfix: if nginx was built with OpenSSL 1.1.0 and used with OpenSSL
1.1.1, the TLS 1.3 protocol was always enabled.
*) Bugfix: working with gRPC backends might result in excessive memory
consumption.
Changes with nginx 1.15.5 02 Oct 2018
*) Bugfix: a segmentation fault might occur in a worker process when
using OpenSSL 1.1.0h or newer; the bug had appeared in 1.15.4.
*) Bugfix: of minor potential bugs.
Changes with nginx 1.15.4 25 Sep 2018
*) Feature: now the "ssl_early_data" directive can be used with OpenSSL.
*) Bugfix: in the ngx_http_uwsgi_module.
Thanks to Chris Caputo.
*) Bugfix: connections with some gRPC backends might not be cached when
using the "keepalive" directive.
*) Bugfix: a socket leak might occur when using the "error_page"
directive to redirect early request processing errors, notably errors
with code 400.
*) Bugfix: the "return" directive did not change the response code when
returning errors if the request was redirected by the "error_page"
directive.
*) Bugfix: standard error pages and responses of the
ngx_http_autoindex_module module used the "bgcolor" attribute, and
might be displayed incorrectly when using custom color settings in
browsers.
Thanks to Nova DasSarma.
*) Change: the logging level of the "no suitable key share" and "no
suitable signature algorithm" SSL errors has been lowered from "crit"
to "info".
Changes with nginx 1.15.3 28 Aug 2018
*) Feature: now TLSv1.3 can be used with BoringSSL.
*) Feature: the "ssl_early_data" directive, currently available with
BoringSSL.
*) Feature: the "keepalive_timeout" and "keepalive_requests" directives
in the "upstream" block.
*) Bugfix: the ngx_http_dav_module did not truncate destination file
when copying a file over an existing one with the COPY method.
*) Bugfix: the ngx_http_dav_module used zero access rights on the
destination file and did not preserve file modification time when
moving a file between different file systems with the MOVE method.
*) Bugfix: the ngx_http_dav_module used default access rights when
copying a file with the COPY method.
*) Workaround: some clients might not work when using HTTP/2; the bug
had appeared in 1.13.5.
*) Bugfix: nginx could not be built with LibreSSL 2.8.0.
Changes with nginx 1.15.2 24 Jul 2018
*) Feature: the $ssl_preread_protocol variable in the
ngx_stream_ssl_preread_module.
*) Feature: now when using the "reset_timedout_connection" directive
nginx will reset connections being closed with the 444 code.
*) Change: a logging level of the "http request", "https proxy request",
"unsupported protocol", and "version too low" SSL errors has been
lowered from "crit" to "info".
*) Bugfix: DNS requests were not resent if initial sending of a request
failed.
*) Bugfix: the "reuseport" parameter of the "listen" directive was
ignored if the number of worker processes was specified after the
"listen" directive.
*) Bugfix: when using OpenSSL 1.1.0 or newer it was not possible to
switch off "ssl_prefer_server_ciphers" in a virtual server if it was
switched on in the default server.
*) Bugfix: SSL session reuse with upstream servers did not work with the
TLS 1.3 protocol.
Changes with nginx 1.15.1 03 Jul 2018
*) Feature: the "random" directive inside the "upstream" block.
*) Feature: improved performance when using the "hash" and "ip_hash"
directives with the "zone" directive.
*) Feature: the "reuseport" parameter of the "listen" directive now uses
SO_REUSEPORT_LB on FreeBSD 12.
*) Bugfix: HTTP/2 server push did not work if SSL was terminated by a
proxy server in front of nginx.
*) Bugfix: the "tcp_nopush" directive was always used on backend
connections.
*) Bugfix: sending a disk-buffered request body to a gRPC backend might
fail.
Changes with nginx 1.15.0 05 Jun 2018
*) Change: the "ssl" directive is deprecated; the "ssl" parameter of the
"listen" directive should be used instead.
*) Change: now nginx detects missing SSL certificates during
configuration testing when using the "ssl" parameter of the "listen"
directive.
*) Feature: now the stream module can handle multiple incoming UDP
datagrams from a client within a single session.
*) Bugfix: it was possible to specify an incorrect response code in the
"proxy_cache_valid" directive.
*) Bugfix: nginx could not be built by gcc 8.1.
*) Bugfix: logging to syslog stopped on local IP address changes.
*) Bugfix: nginx could not be built by clang with CUDA SDK installed;
the bug had appeared in 1.13.8.
*) Bugfix: "getsockopt(TCP_FASTOPEN) ... failed" messages might appear
in logs during binary upgrade when using unix domain listen sockets
on FreeBSD.
*) Bugfix: nginx could not be built on Fedora 28 Linux.
*) Bugfix: request processing rate might exceed configured rate when
using the "limit_req" directive.
*) Bugfix: in handling of client addresses when using unix domain listen
sockets to work with datagrams on Linux.
*) Bugfix: in memory allocation error handling.
Development branch changes are made every few weeks and stable branch changes are made less often.
Updating Nginx
Normally you update Nginx bu running an update and upgrade
Restart Nginx for good measure
Checking NGINX Version
Changing your repository to the development branch
I changed ot the development branch by running
Update and upgrade Nginx
Restart Nginx for good measure
Checking NGINX Version
Removing the stable Nginx repository
Run this command to remove the stable branch of Nginx
Check to see if the development branch is listed
Good luck and I hope this guide helps someone
Ask a question or recommend an article
[contact-form-7 id=”30″ title=”Ask a Question”]
Revision History
v1.0 Initial post